Welcome to the Cyber Security Multi-Factor Authentication (MFA) webpage. From here you can access information and services to help you understand, set up, and use MFA.
Multi-Factor Authentication at UNSW
Multi-Factor Authentication is a requirement at UNSW for all students and staff (including casuals and affiliates), i.e., everyone with a current zID account. MFA provides an additional layer of security to help protect the University and your account from unauthorised access.
Our University uses Microsoft Authenticator app, which needs to be installed on your smartphone before completing the MFA registration on your computer. Once set up, MFA will periodically prompt you to verify your sign-in to single sign-on (SSO) applications such as Outlook, Moodle, and SharePoint.
New Students and staff will be prompted to set up MFA as part of their onboarding processes. MFA also applies to staff with a zID_sa account.
- Refer to the Cyber Security Policies and Standards that support user access.
- Refer to the Single Sign-On website for more information about SSO applications.
- Refer to the MFA security update for February 2023 (Inside UNSW news)
Watch this video to understand MFA and an overview of the set up process.
MFA combines two or more sets of credentials; what you know, such as your password, and what you have such as a Microsoft Authenticator app on your smartphone. The goal of MFA is to create an additional layer of defense to make it more difficult for unauthorised people to access the University’s resources (data, applications or devices) via your zID account.
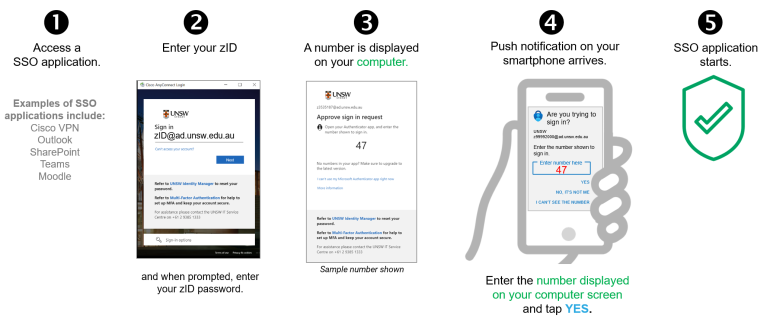
After signing in using your zID and password, you may be prompted by the Microsoft Authenticator app (push notification) to verify that it is you signing in. A 2-digit number will appear on your sign-in device (eg computer), which you then need to enter into the app on your smartphone. Tap Yes (or Done) to confirm it is you and the University single sign-on (SSO) application will open.
If you receive a push notification on your smartphone but you know it isn't you signing in, please tap No, It’s Not Me. At this point a Report Fraud/Suspicious Activity message will appear. You can then select ‘Report’ and the fraud attempt will be sent to UNSW IT Cyber Security Operations team for investigation. If in doubt, report it! (Accidental alerting is expected, and no one will get in trouble).
The rules
MFA is only applied to a zID when it accesses a UNSW single sign-on (SSO) application. Examples of SSO applications include Office 365 (Outlook, Teams, etc), Moodle, SharePoint, etc.
The majority of users will be prompted to verify at least once every 30 days per device used when accessing an SSO application and more often when accessing applications with a higher risk profile, such as the VPN which will prompt for MFA more frequently (e.g. 12 hours). Thereafter you will be prompted again to verify only if;
- You use a new browser,
- You clear your browser cookies/cache,
- You use another computer such as one found on a lectern,
- You work from a new location,
- You use a new Wi-Fi connection, or
- Our MFA solution considers that a risk-based event may have occurred.
|
Important:
|
Refer to the Support Materials section of this page for guides to help you use MFA.
MFA is only applied to a zID when it accesses a UNSW single sign-on (SSO) application. Examples of SSO applications include Office 365 (Outlook, Teams, etc), Moodle, SharePoint, etc.
The one-off setup process first requires the installation of the Microsoft Authenticator app on your smartphone before completing the MFA registration on your computer. Watch the 3-minute video (click on the image to the left) to gain an overall understanding.
To set up MFA, you will need to:
|
Smartphone |
|
| Computer |
|
| Time |
|
To Start: follow the step-by-step guide and set up MFA. Note: if the Microsoft Authenticator app is unavailable in your smartphone’s app store, follow this guide to set up MFA.
- Do not uninstall the Microsoft Authenticator app as you will need it to verify your sign-in when prompted periodically. Refer to the guide to use MFA.
- Always have your authenticator (smartphone or YubiKey) with you when accessing University single sign-on applications.
Refer to the Support Materials section on this page for further guides and FAQs.
(Optional) Setup an MFA back up option
Microsoft Authenticator app can be installed on another smartphone or mobile device, such as an iPad, and that device is then used as your backup. For example, when you have forgotten or lost your smartphone you could use your iPad.
Note: Microsoft Authenticator app cannot be installed on your computer or laptop.
Refer to the guide to set up MS Authenticator app on a second mobile device and use it as a backup.
Microsoft Authenticator
Microsoft Authenticator app is the supported authenticator used by the University. Set up MFA by installing the Microsoft Authenticator app on your smartphone and completing the one-off registration on your computer. As soon as you set up MFA, it will be enabled for your zID.
Benefits of using the Microsoft Authenticator include:
- Easy to use via the push notification feature of the Microsoft Authenticator app.
- Free and available for Android and Apple smartphones.
- The app takes up minimal space on your device.
- The app uses minimal battery.
- The app does not have access to your phone data/apps. Refer to the Tips and Privacy Information section on this website.
- The app can be installed on other mobile devices (e.g., an iPad) as a backup.
- Verification can operate without an internet connection by way of a One-Time Password code stored within the Microsoft Authenticator app.
Refer to the Support Materials section of this page for answers to frequently asked questions.
YubiKey
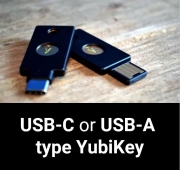
A YubiKey is a physical security token and is an alternative where:
- Your work/study circumstances do not allow you to use your smartphone in certain environments,
- You don’t have a smartphone,
- Your smartphone operating system cannot be upgraded to the version supported by the Microsoft Authenticator app, or
- You decline to use your personal smartphone for work/study purposes.
Limitations will apply, such as:
- UNSW provided YubiKeys are the property of the University and lost devices may incur a cost.
- The act of verifying your sign-in requires the YubiKey to be plugged into the computer, entering your PIN and tapping the YubiKey.
- You must remember to carry your YubiKey everywhere when you access a University single sign-on application.
- UNSW-provided YubiKeys must be returned to the IT Service Centre when not required or the individual leaves UNSW.
Requesting a YubiKey
- Staff and Students are to call the IT Service Centre on (02) 9385 1333 to enquire about alternatives or understand the full limitations and conditions of using a YubiKey.
- Staff can request a UNSW-provided YubiKey by calling the IT Service Centre. The YubiKey can be picked up from the Upper Campus IT Hub walk-in service centre located in Room G06, D26 Biological Sciences Building (next door to XS cafe). ID verification will be required.
- Students who cannot use the Microsoft Authenticator app are requested to upgrade their smartphone's operating system to the latest version, and then install the Microsoft Authenticator app. If this is not possible, students can:
- Use their own Yubikey (Series 5) for authentication (independently purchased); or
- Seek further assistance via the Nucleus Student Hub (Sydney students) or Student Administrative Services (Canberra students) or refer to the support and development services available.
Important:
- Do not use the general IT service request option to open a service ticket or email your request for a YubiKey. ID verification is required by the UNSW IT Service Center and therefore all requests need to be via a phone call or in person.
- Once you have your YubiKey, contact the IT Service Centre for a TAP code. needed to set up your YuibKey.
- The TAP code is valid for 7 days. If the TAP code expires or you forget the code, you will need to call the UNSW IT Service Centre for a new TAP code to be issued. ID verification will be required.
As soon as you receive your YubiKey, follow the respective YubiKey setup guides found under the Support Materials section of this page.
When switching phones, simply transferring data/photos (or a backup/restore) from your old phone to your new phone won’t re-establish your MFA account. Note: You may see the Microsoft Authenticator app (and account) on your new smartphone, but they will not work.
If you still have access to your old phone:
Please follow the steps in this guide (requires both your old and new phone): Transfer the Microsoft Authenticator app to a new phone (PDF, 922KB) prior to factory resetting your old phone.
If you no longer have access to your old phone:
You need to request an MFA Reset. Please contact the IT Service Centre via Phone: (02) 9385 1333 or visit in person at one of the IT walk-in service centres. Note: ID verification will be required.
Support materials
Access frequently asked questions (FAQs), how-to guides, tips to help you use MFA, and links to privacy and accessibility information.
Answers to questions regarding the setup and use of MFA, via MS Authenticator or a YubiKey.
How-to guides
- Set up MFA using Microsoft Authenticator (PDF, 1240KB) on your smartphone.
- Set up MFA when Microsoft Authenticator is unavailable in your smartphone app store (PDF, 1353KB) Note: This guide may be useful to China-based students.
- Set up MS Authenticator app on a second mobile device (PDF, 916KB) as a backup, after setting up MFA on your primary mobile device.
- Use Microsoft Authenticator (PDF, 1281KB)
- Use Microsoft Authenticator without a data/internet connection (PDF, 772KB) or when push notifications are unavailable.
- Transfer the Microsoft Authenticator app to a new phone (PDF, 1067KB) from your old phone (before you throw out your old phone).
- Set up and use a YubiKey (PDF, 1284KB)
- Set up and use a YubiKey for non-Windows devices (PDF, 1.17MB) such as Mac and Linux.
Videos
Privacy information
- Refer to the MFA using Microsoft Authenticator Privacy Statement for details about the personal information collected by Microsoft Authenticator.
- Refer to the student privacy statement or privacy policy for UNSW staff.
MFA Tips
- Carry your authenticator (smartphone or YubiKey) when accessing University single sign-on (SSO) applications.
- Do not uninstall the app from your smartphone. You need it to verify when accessing University SSO applications on an ongoing basis. If you do uninstall it by accident, call the UNSW IT Service Centre for an MFA reset and then redo the setup.
- Set up Microsoft Authenticator app on another mobile device as a backup when you don’t have your smartphone with you.
- Transfer your Microsoft Authenticator account from your old smartphone to your new smartphone before you get rid of your old smartphone.
- UNSW provided YubiKeys must be returned when you leave the University.
The Microsoft Authenticator app is compliant with the global W3C Web Content Accessibility Guidelines (WCAG) 2.1, which also applies to mobile web apps. The WCAG guideline explains how all digital content is more accessible to people with disability. One of the key objectives of the guidelines is to ensure that the Microsoft Authenticator app content is directly accessible.
Quick reference guide of the WCAG 2.1 supported features:
MFA accessibility is based on the principles of ‘Perceivable’, ‘Operable’ ‘Understandable’ and ‘Robust’, which include the following supported features:
Perceivable
- Provide text alternatives for non-text content.
- Provide captions and other alternatives for multimedia.
- Create content that can be presented in different ways, including by assistive technologies, without losing meaning.
- Make it easier for users to see and hear content.
Operable
- Make all functionality available from a keyboard.
- Give users enough time to read and use the content.
- Do not use content that causes seizures or physical reactions.
- Help users navigate and find content.
- Make it easier to use inputs other than the keyboard.
Understandable
- Make text readable and understandable.
- Make content appear and operate in predictable ways.
- Help users avoid and correct mistakes.
Robust
- Maximize compatibility with current and future user tools.
Exemption Process
If you have accessibility issues with using MFA, that is preventing you from being able to work. You can request an exemption from the Access, Equity and Inclusion Team.
MFA support
For MFA technical issues and assistance contact the IT Service Centre:
Phone: (02) 9385 1333 and select MFA from the options presented to reach the dedicated support team.
Email: itservicecentre@unsw.edu.au for non-urgent questions.
- ID verification may be required pending your issue/request and therefore, if possible, please call the IT Service Centre or visit in person at one of the IT walk-in service centres.
- Staff or Students need to first call the IT Service Centre to understand the full limitations and conditions of using a YubiKey. Please read the Your MFA Alternatives section on this page for YubiKey information.